Controlled connectivity
Defined audio, video and display paths replace unmanaged source handling, wireless casting and uncertain room behaviours.

SECURE CONTROL ROOM
Protected inputs. Encoded streams. Twin output paths to video wall and operator monitor — all under unified control.
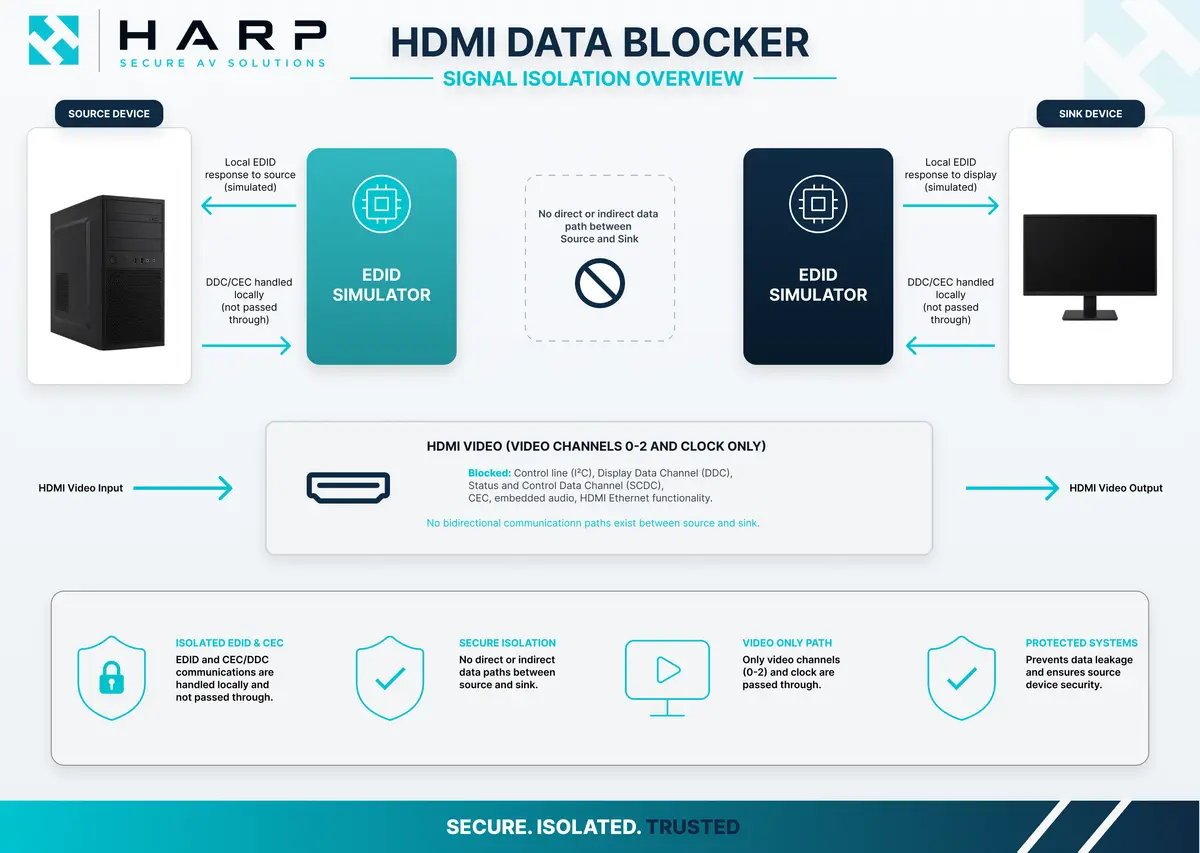
Physical display interfaces can sit outside normal IT security controls. In defence, secure briefing and regulated operational environments, unmanaged HDMI connections may create an unintended communication path between connected systems.
The Harp Visual HDMI Data Blocker enforces a hardware boundary at the HDMI interface. Designed and manufactured in the UK, it supports secure AV use cases where visual output needs to be controlled without relying on software policy or user behaviour.
MERLIN is Harp Visual's UK-designed and manufactured video wall processor for control rooms, command environments and knowledge walls where multiple sources need to be presented clearly and reliably.
It supports secure AV and operational display workflows by giving teams controlled source management, video wall layout control and a processor platform designed around continuous room operation.

In secure control rooms, an operator often needs to work across computers on different networks — classified, unclassified, internet-connected, air-gapped. The Secure KVM lets them drive every machine from one keyboard, mouse and monitor while guaranteeing, at a hardware level, that no data ever crosses between the connected systems.
Certified to NIAP Common Criteria Protection Profile for Peripheral Sharing Devices v4.0 and listed on the NATO NIAPC Product Registry. Data path isolation and unidirectional data flow are enforced by hardware. Chassis intrusion detection is always on. Switching is manual only — there is no software interface, no network port, and no firmware update path.

Acoustic Privacy / Sound Masking
Sensitive conversations create their own attack surface. In secure briefing rooms, executive offices and operational spaces, deliberate eavesdropping — and accidental overhearing through walls, ducts and shared structures — can compromise confidential information just as effectively as a network breach. Acoustic privacy hardware addresses the threat at the source.
The Cambridge family from Biamp covers both ends of the problem. Sound masking emitters add a precisely-engineered ambient sound that makes nearby speech unintelligible without being intrusive. Dedicated eavesdropping protection systems — innovated and refined since 1975 — protect against intentional audio surveillance through pipes, ducts, walls and shared building structures. The same range is used to protect corporate intellectual property, mission-critical discussions and national security conversations.

Secure AV is the controlled connectivity layer for rooms where what is connected, displayed and shared needs to be predictable.
Defined audio, video and display paths replace unmanaged source handling, wireless casting and uncertain room behaviours.
Presentation, briefing and video conferencing infrastructure designed around information handling and room security requirements.
HDMI Data Blockers and other hardware controls can enforce boundaries where software policy alone is not appropriate.
Rooms can be delivered without WiFi or Bluetooth where wired-only connectivity is part of the requirement.
Secure AV is the practical discipline of making room connectivity predictable in controlled environments.
Standard AV often relies on general-purpose hardware, unmanaged display interfaces and connectivity features such as wireless casting, HDMI plug-and-play and consumer control protocols.
In rooms where information handling, access control and operational security matter, those assumptions need to be revisited before equipment is specified.
Secure AV starts with who uses the room, what information is handled, what connections are permitted and what unintended data flow would mean. Signal paths and room behaviours are then designed around that model.
Secure AV principles apply wherever organisations need predictable, controlled AV behaviour - not just in the most sensitive environments.





The specific requirements depend on the room, its users and its information context. These are the design principles Harp Visual applies consistently across secure and managed AV environments.
Audio, video and display signals follow defined routes between sources, processors, displays and room systems. Unintended signal paths are designed out - not managed through procedure.
Users have clear, repeatable connection options and room behaviour. Unmanaged source handling - wireless casting, consumer HDMI plug-and-play, uncontrolled visitor device connections - is removed or controlled where the environment requires it.
Displays show the right sources to the right audience. What is presented, to whom and from which source is controlled by the room design - not left to user discretion.
Where software policy alone is insufficient, hardware-based controls - such as the HDMI Data Blocker - enforce signal boundaries at the interface level. No reliance on user action or configuration.
Secure AV systems can be delivered without WiFi or Bluetooth where the environment requires controlled, wired-only connectivity. Wireless presentation casting is removed from rooms where it is not appropriate.
System design aligns with applicable MOD, NCSC and secure infrastructure guidance where required - including Secure by Design principles, physical infrastructure security and equipment containment practices.
Signal distribution is part of the assurance model, not a technical detail to resolve after the displays are chosen.
The way AV signals move across a room or facility is a fundamental part of system design.
Architecture choices depend on assurance requirements, operational context and the configuration of the facility.
Harp Visual designs and delivers three distinct AV distribution architectures for secure and operational environments.
A completely isolated AV network with no connection to any external network - building LAN, internet or otherwise. Sources, encoders, processors, transmitters, receivers and displays all operate on a physically separate, dedicated network that exists only within the room or facility. Nothing enters or leaves that network by design. This is a high-assurance AV architecture - appropriate for environments where the risk of unintended external connectivity cannot be accepted, and where the accreditation process benefits from a clearly bounded, standalone system. Common in defence command rooms, intelligence environments, secure briefing suites and other high-assurance operational spaces.
AV signals distributed over IP on a dedicated, physically segregated network within a single building or facility. Managed switching, VLAN segmentation and controlled traffic handling ensure the AV network operates independently of the building LAN and any external connectivity. More scalable than a fully closed loop architecture - supporting multiple rooms, operator positions and display environments within the same facility from a single controlled infrastructure. The Harp Visual MERLIN IPX processor is specifically designed for AV-over-IP environments - encoding, distributing and managing sources across the network with controlled routing and flexible display management.
AV signals distributed over IP across multiple buildings, sites or facilities - extending operational display capability beyond a single room or location. Live sources presented at remote operator positions, mirrored display environments and distributed control room architectures all become possible within a controlled IP infrastructure. Multi-facility AV-over-IP is delivered subject to the co-operation and approval of the client's IT and security teams, with the AV network architecture designed in alignment with the wider network security requirements of the organisation. Appropriate for transport network operations, utility infrastructure monitoring, multi-site defence programmes and enterprise operations across distributed estates.
Secure AV projects are delivered with the same rigour applied to Harp Visual control room and defence infrastructure work.
Delivery includes a Method Statement and RAMS, with pre-configuration completed off-site before site attendance.
Systems are delivered with structured rack builds, labelled terminations, managed switch configuration and a post-installation as-fitted schematic.
Support includes same-business-day remote response, next-working-day attendance where required, fault diagnosis, firmware management, configuration changes and annual health checks.
Room layouts, signal paths, source routing, interface controls and connectivity options designed around the operational and security model - before any equipment is specified.
Video conferencing platforms integrated into controlled room designs. Wired presentation workflows. Managed audio and camera systems configured for stable, professional operation in senior briefing and formal meeting environments.
Hardware-enforced interface control at HDMI connections - between sources and displays, between visitor devices and room systems, between classification domains. Specified as part of the wider room architecture, not retrofitted.
AV systems designed without WiFi or Bluetooth where the environment requires it. Wired-only signal distribution, structured cabling and managed connectivity throughout.
Pre-configuration off-site, structured on-site installation, end-to-end functional testing, operator walkthrough and post-installation as-fitted documentation.
3-year support programme including remote response, on-site attendance, firmware and configuration management, preventative maintenance and user training.
Secure AV delivery brings together Harp Visual products and carefully specified supporting infrastructure for controlled, operational room environments.





Support is scoped around the system, the environment and the operational requirement.
Support packages can include proactive maintenance visits, firmware and software management, and system configuration support.
Options include 4-hour physical attendance in the UK where contracted and a 24/7 engineer-manned service desk.
Fault diagnosis and repair are scoped around the delivered system, the room environment and the operational requirements of the organisation.
Direct answers for teams assessing secure AV, video conferencing and controlled collaboration rooms.
Secure AV is the design and integration of audio, video, conferencing and display systems with controlled signal paths and predictable room behaviour. It applies to environments where organisations need to control what is connected, routed, displayed and shared - and where standard AV design assumptions are not appropriate.
Yes. AV systems can be designed without WiFi or Bluetooth where the environment requires wired-only, controlled connectivity. This includes video conferencing, presentation and display systems delivered as fully wired installations with no wireless interfaces.
Visitor and contractor HDMI connections can be controlled using the Harp Visual HDMI Data Blocker, placed inline between the laptop connection and the room display or switcher. This allows normal presentation use while removing the unmanaged HDMI interface risk - with no configuration or user action required.
Harp Visual aligns AV system design with applicable MOD and secure infrastructure guidance relating to physical infrastructure security, structured cabling practice, equipment containment, serviceability and risk reduction. Secure by Design principles are applied to system architecture where applicable. All installation work is delivered with Method Statement, RAMS and post-installation as-fitted documentation.
Secure AV projects can consider TAA-compliant and specified country-of-origin requirements during product selection where these form part of the deployment specification. Suitability depends on the products, deployment context and customer requirements. Contact Harp Visual to discuss your specific procurement constraints.
Harp Visual provides a structured managed support programme including same business day remote response, next working day on-site attendance where required, firmware and configuration management, preventative maintenance and user training. Support is scoped to the specific system and environment.
A closed loop AV system is a completely isolated AV network with no connection to any external network - building LAN, internet or otherwise. All sources, processing and displays operate on a physically separate, dedicated network. This is a high-assurance AV architecture - appropriate for environments where unintended external connectivity cannot be accepted and where the system needs to operate as a clearly bounded, standalone installation. Closed loop systems are also referred to as air-gapped AV systems.
An air-gapped AV system is a closed loop AV installation with no physical or logical connection to any external network. The term air-gapped refers to the absence of any network connection between the AV system and external infrastructure - the gap between them is, in effect, air. Air-gapped AV is commonly specified in defence command environments, intelligence facilities, secure briefing suites and other high-assurance operational spaces where the risk of unintended connectivity needs to be reduced by design rather than managed by policy.
Secure AV-over-IP is the distribution of AV signals over an IP network - but on a dedicated, physically segregated network rather than a shared building LAN. Managed switching, VLAN segmentation and controlled traffic handling ensure the AV network operates independently and securely. Harp Visual designs secure AV-over-IP systems for single-facility environments and, subject to IT and security team co-operation, for multi-facility or multi-site operational deployments. The MERLIN IPX processor is specifically built for AV-over-IP environments.
A closed loop or air-gapped system has no external network connection whatsoever - the AV network is physically isolated. An AV-over-IP system distributes signals over IP but on a dedicated, controlled network that is segregated from external connectivity. Closed loop offers a simpler accreditation boundary. AV-over-IP offers greater scalability - supporting multiple rooms, buildings or sites - but requires appropriate network architecture and security controls. The right choice depends on the assurance requirements, operational context and facility configuration of the specific environment.
Talk to Harp Visual about your room, your operational context and what controlled AV connectivity needs to support. We can discuss signal path design, interface security, conferencing integration and long-term support - from initial design through to delivery and ongoing maintenance.